Table of Contents
In this article, I will take you through the steps to enable root user for ssh authentication on Ubuntu 20.04 LTS. If you are Linux user or professional then you might be aware that by default on Ubuntu based systems, root user will not be enabled for ssh authentication due to security purposes. You always need to login with non-root user account and then if you need you can switch to root user after providing correct credentials.
While in most of the cases this works really well but some times you might get a situation when you need to have direct root user access to perform some important task. In those situations, you need to enable root user for SSH authentication. This can be easily done using steps shown in below section. More about SSH Protocol.
How to Enable root user for SSH Authentication on Ubuntu 20.04 LTS
Also Read: Best Steps to Install Perl on Rocky Linux 8
Step 1: Prerequisites
a) You should have a running Ubuntu 20.04 LTS System.
b) You should have sudo or root access to run privileged commands.
c) You should have OpenSSH Server installed in your System.
Step 2: Edit /etc/ssh/sshd_config File
By default if you have check PermitRootLogin parameter using grep -i permitrootlogin /etc/ssh/sshd_config command then you will see it is set as prohibit-password. You need to change this parameter to yes to enable root user authentication.
root@localhost:~# grep -i permitrootlogin /etc/ssh/sshd_config
PermitRootLogin prohibit-password
# the setting of "PermitRootLogin without-password".
For that you need to open /etc/ssh/sshd_config file using our favorite nano editor and then set the parameter value to yes. Then Press Ctrl+X and give Y to save and close the file.
root@localhost:~# nano /etc/ssh/sshd_config # $OpenBSD: sshd_config,v 1.103 2018/04/09 20:41:22 tj Exp $ # This is the sshd server system-wide configuration file. See # sshd_config(5) for more information. # This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin # The strategy used for options in the default sshd_config shipped with # OpenSSH is to specify options with their default value where # possible, but leave them commented. Uncommented options override the # default value. Include /etc/ssh/sshd_config.d/*.conf #Port 22 #AddressFamily any #ListenAddress 0.0.0.0 #ListenAddress :: #HostKey /etc/ssh/ssh_host_rsa_key #HostKey /etc/ssh/ssh_host_ecdsa_key #HostKey /etc/ssh/ssh_host_ed25519_key # Ciphers and keying #RekeyLimit default none # Logging #SyslogFacility AUTH #LogLevel INFO # Authentication: #LoginGraceTime 2m PermitRootLogin yes #StrictModes yes #MaxAuthTries 6 #MaxSessions 10
After changing the parameter, you can verify it by again by using the same grep -i permitrootlogin /etc/ssh/sshd_config command. This time as you can see the value is set as yes. It means allow root user for remote SSH authentication.
root@localhost:~# grep -i permitrootlogin /etc/ssh/sshd_config
PermitRootLogin yes
# the setting of "PermitRootLogin without-password".
Step 3: Restart SSH service
After setting the parameter, you need to restart ssh service by using systemctl restart ssh command as shown below.
root@localhost:~# systemctl restart ssh
Then check the service status by using systemctl status ssh command. It should show as active and running as you can see below.
root@localhost:~# systemctl status ssh
● ssh.service - OpenBSD Secure Shell server
Loaded: loaded (/lib/systemd/system/ssh.service; enabled; vendor preset: enabled)
Active: active (running) since Fri 2021-11-05 09:03:42 IST; 12min ago
Docs: man:sshd(8)
man:sshd_config(5)
Process: 3873 ExecStartPre=/usr/sbin/sshd -t (code=exited, status=0/SUCCESS)
Main PID: 3875 (sshd)
Tasks: 1 (limit: 2312)
Memory: 2.5M
CGroup: /system.slice/ssh.service
└─3875 sshd: /usr/sbin/sshd -D [listener] 0 of 10-100 startups
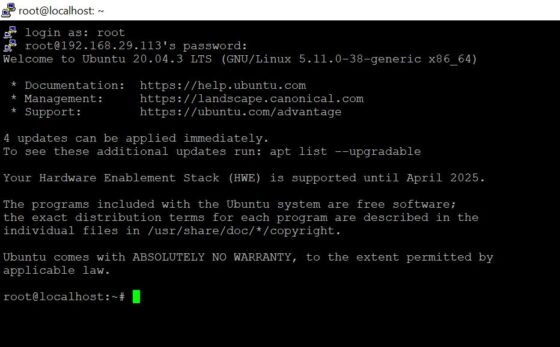
Step 4: Login with root
Now you can try login with root user account using putty or any other SSH tools you are using. Here we are using putty application so we will connect our Server by providing its IP Address 192.168.29.113. It will then ask for login user which will be root and then provide the root password to authenticate. It should login successfully as shown below.
Step 5: Reset root password(Optional)
Sometimes you might face Access Denied error even after changing PermitRootLogin parameter to yes and restarting the ssh service. In that situation, you can reset root user password once by using passwd command and then try with the new password.
root@localhost:~# passwd
New password:
Retype new password:
passwd: password updated successfully
